Identity and Agentic ID Governance
Govern humans, services, and AI agents under one Apporetum control plane on Microsoft Entra, with Identity Observability across every grant, transition, and anomaly.
AI agents are identities, and your governance model has to catch up.
The number of non-human identities in a typical Microsoft 365 tenant is now larger than the workforce headcount: Azure service principals, managed identities, Power Platform connectors, Microsoft 365 Copilot agents, custom Graph applications, and an accelerating wave of third-party AI agents. Each is an identity that requests access, holds entitlements, and acts inside your estate, often with permissions broader than the person who deployed it. Identity and Agentic ID Governance brings the same JML, certification, and audit discipline to every identity type.
JML for human & non-human identities
Identity types Apporetum governs:
Workforce identities
Employees and internal staff: full deterministic JML, manager reviews, role mining, and ISO 27001-aligned audit evidence.
Contractor & B2B identities
Contractors, partners, and B2B guests on Entra ID: bounded contracts, mandatory expiry, sponsor-led renewals.
Secondary admin accounts
Personal admin accounts and privileged accounts: stricter guardrails, shorter review intervals, mandatory PIM eligibility.
Service principals & managed identities
Azure service principals, managed identities, workload identities, and custom Graph applications: first-class governance type.
AI agents & Copilot agents
Microsoft 365 Copilot agents, Power Platform connectors, and third-party AI agents: owner-attributed, time-bound, behaviour monitored.
Bot & service accounts
Legacy bot accounts and shared service accounts: surfaced, correlated to a human owner, and time-bound or migrated to a managed identity.
Identity Observability: see every grant, transition, and anomaly.
Most identity stacks log events. Apporetum's Identity Observability turns those events into a usable picture: per-identity membership timelines, baseline behavioural patterns for each identity type, drift between granted and actually-used permissions, and anomaly alerts when an identity acts out of its own pattern.
Identity Observability runs across humans, services, and AI agents from the same telemetry pipeline. You answer "what changed for this agent in the last 30 days?" the same way you answer the question for a person.
Identity & Access Insights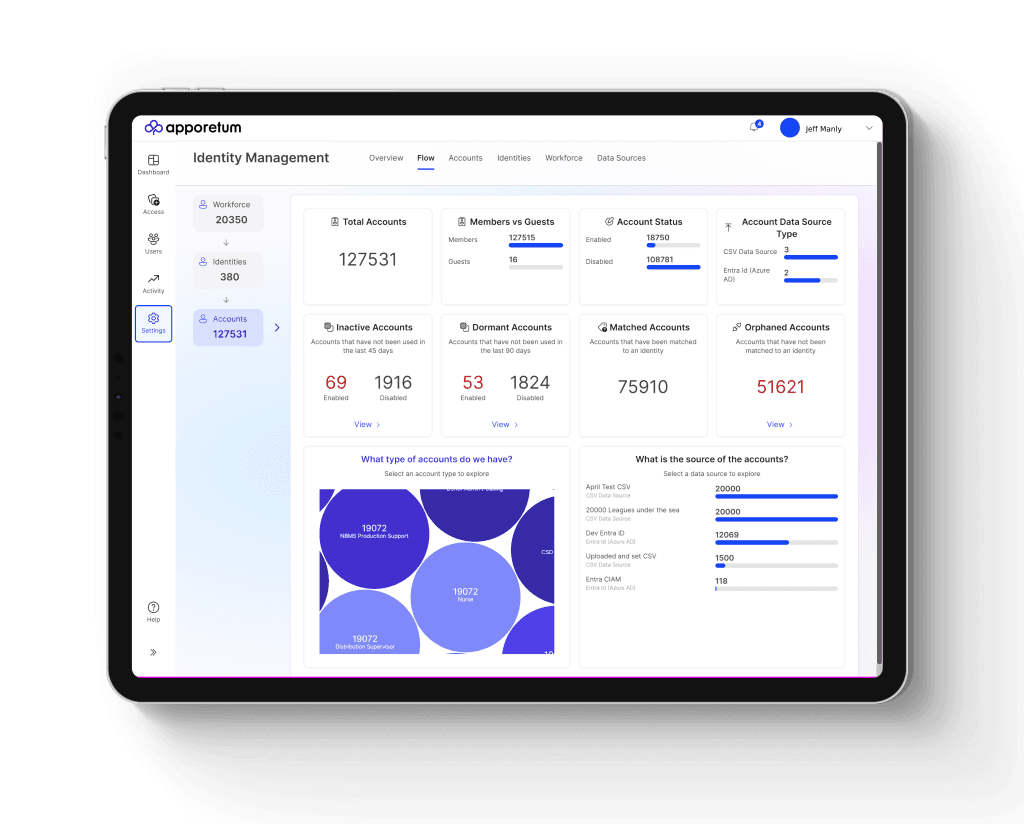
Membership timelines
Every grant, revocation, review decision, and lifecycle transition on a single per-identity timeline, whether human, service, or agent.
Behavioural baselines
Apporetum learns the access pattern of each identity type so outliers (such as an agent suddenly enumerating mailboxes) stand out instead of getting lost in the log volume.
Drift & anomaly alerts
Surface unused entitlements, dormant service principals, and agents whose actual API usage exceeds what was approved at grant time.
Orphan detection
Service principals and bot accounts without an owner are surfaced, attributed back to a human owner, or scheduled for expiry.
Cross-tenant observability
Identity Observability spans every connected Entra tenant. A human or service identity exhibiting unusual cross-tenant behaviour is visible in one place.
SIEM forwarding
Stream events to Microsoft Sentinel or your SIEM of choice. Apporetum is the source-of-record; your SOC keeps using its existing tools.
Governance controls that apply to every identity type
The same governance primitives Apporetum applies to a workforce identity also apply to a service principal or an AI agent. That consistency is the point: auditors get one story, not three.
JML state machines
Joiner, mover, leaver, suspend, archive: modelled per identity type. Agents get hire-to-retire too.
Time-bound access
No identity gets indefinite access. Renewals are explicit and owner-attributed, agents and services included.
Guardrails & SoD
Segregation-of-duty and contract-type rules are enforced at the moment of assignment, for humans, services, and agents alike.
Owner attribution
Every non-human identity has a human owner who is accountable for its scope and renewal. Owners cycle out cleanly via JML.
Access certifications
The same review campaign covers a person's entitlements, a service principal's API permissions, and an agent's tool-use scopes.
Membership audit trail
Per-entitlement audit (granted, by whom, under what policy, reviewed, revoked), ISO 27001 / SOC 2 / Essential Eight aligned.
Continuous reconciliation
Apporetum re-checks every assignment against current policy and actual usage. Drift surfaces before audit, not at audit.
Identity and Agentic ID Governance, with Identity Observability built in.
One control plane for every identity in your Microsoft Entra estate. Flat-fee subscription, no per-user licensing, no separate SIEM purchase required.